 At Web2Expo this week, I chatted with Kevin Weil, who runs analytics at Twitter. We’ll publish the interview in audio form here soon, but one of the most interesting things I learned from him was how Twitter infers a relationship. Not all followers are equal, apparently.
At Web2Expo this week, I chatted with Kevin Weil, who runs analytics at Twitter. We’ll publish the interview in audio form here soon, but one of the most interesting things I learned from him was how Twitter infers a relationship. Not all followers are equal, apparently.
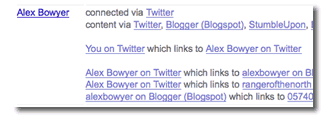
- If there’s a symmetric follow between two people, Twitter assumes they know one another and the relationship is conversational.
- On the other hand, if it’s a one-way relationship — I follow the Bay Bridge, but it doesn’t follow me back — then Twitter assumes the relationship is around subject matter (in other words, I want the traffic updates from the bridge.)
 Does this mean that if you’re the kind of person who follows everyone back, you’re not thought of as a subject matter expert? If so, expect a rash of unfollowing as users tweak their online profiles.
Does this mean that if you’re the kind of person who follows everyone back, you’re not thought of as a subject matter expert? If so, expect a rash of unfollowing as users tweak their online profiles.
As Twitter’s opinion of us becomes increasingly important for things like advertising effectiveness, people are bound to try and game the system. Analysis of social graphs will be part of an arms race similar to that seen in Search Engine Optimization, where unscrupulous marketers try to convince Google to list them in search results. Call it Social Graph Optimization (SGO).





 @
@ Tags:
Tags: 






 Like all images on the site, the topic icons are based on images used under Creative Commons or in the public domain. Originals can be found from the following links. Thanks to
Like all images on the site, the topic icons are based on images used under Creative Commons or in the public domain. Originals can be found from the following links. Thanks to